Facts on Offensive or Obscene Content



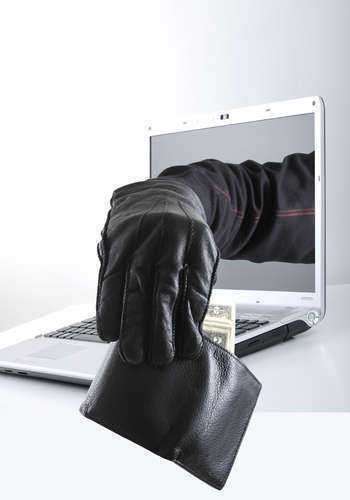
Computer fraud is a common type of computer crime and it can be executed in many different ways. Computer fraud (also known as internet fraud) is often committed when a criminal hacks into an account to gain access to information that they would normally not have permission to obtain. Internet fraud is often used to deceive a third party through use of the internet in order to achieve financial gain. As far as financial gain is concerned, the criminal may hack into another person's bank account, credit card account, or even steal information in order to obtain a loan.
However, fraud can also be used as a way to commit sabotage against an individual or a place of business. In some cases, the criminal has a personal vendetta against an individual(s) or place of business, the hacker will gain access into an account to create chaos and harm to the victim. The harmful spread of false e-mails could also be considered a form of fraud.
Many times, computer fraud/internet fraud is closely related to identity fraud, in that both of these methods involve illegally obtaining information via the internet and using it to deceive others. However, identity theft is more specific in that it actually includes an individual posing as another person or entity in order to achieve some sort of personal agenda. Identity theft can be considered a form of computer fraud and it is usually used as means to gain materials or finances. Legal action might take place with the assistance of a fraud lawyer.
Although a common crime, forms of computer fraud can be avoided. One step that can be taken against falling victim to internet fraud is to refrain from liberally giving out personal information, especially on the computer. This will decrease your chances of a hacker accessing personal accounts.
Another step that can be taken to lessen the chances of such occurrences would be the process of choosing effective usernames and/or passwords. User names and/or passwords should not contain any commonly known facts about the potential victim. Instead, they should be something more abstract and harder to guess. Unfortunately, in many cases, internet fraud victims are actually taken advantage of by someone that is close to them and that knows personal facts. It is vital to avoid using birthdays, social security numbers, etc., within your username and/or password.